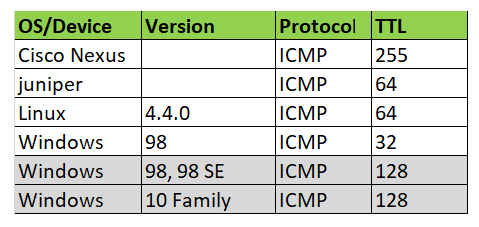
Every packet of data that is sent out includes a TTL value within the IP packet header. This refers to the number of hops data can go through before it is discarded. Based on network traffic between hosts, it is possible to predict what OS is running on a system. Every operating system has its own unique way to implement the TCP/IP stack. A very simple but effective passive method is to inspect the initial time-to-live (TTL) in the IP header:
“Time to live exceeded” this ICMP ping error is due to the time to live (TTL) field reaching a zero value or there is a timeout for the reassembly of segments. As a solution, I will recommend increasing the TTL (Time To Live) value (the highest is 255).
Solution
For example, run traceroute to ipaddress 8.8.8.8 (Google’s publc DNS server). And find number of hops to the destination.
[root@server ~]# traceroute 8.8.8.8 (in linux distro) C:\>tracert 8.8.8.8 (in Windows OS)
For me its 6 hops to 8.8.8.8. So a minimum TTL value of 6 is required to reach icmp packets to 8.8.8.8 and get ping replay. And cannot ping to 8.8.8.8 with a TTL value of 5 or less.
Ping Results with different TTL values:
[root@server ~]# ping 8.8.8.8 -t 5 (-t 5 is for custom TTL value of 5) PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data. From 192.168.1.1 icmp_seq=1 Time to live exceeded From 192.168.1.1 icmp_seq=2 Time to live exceeded From 192.168.1.1 icmp_seq=3 Time to live exceeded From 192.168.1.1 icmp_seq=4 Time to live exceeded
# ping 8.8.8.8 -t 6 (-t 6 is for custom TTL value of 6) PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data. 64 bytes from 8.8.8.8: icmp_req=1 ttl=55 time=48.9 ms 64 bytes from 8.8.8.8: icmp_req=2 ttl=55 time=49.5 ms 64 bytes from 8.8.8.8: icmp_req=3 ttl=55 time=50.4 ms 64 bytes from 8.8.8.8: icmp_req=4 ttl=55 time=49.4 ms