GoBuster is a tool that was built in the Go language, which can be used for brute forcing directories as well as brute forcing subdomains. Since GoBuster is built on Go, we first need to install Go first and then install or configure the GoBuster package. Up until my discovery of Gobuster, I was using tools such as Nikto, Cadaver, Skipfish, WPScan, OWASP ZAP, and DirBuster. Every one of these tools has its strengths and weaknesses but, in the end, they all worked pretty much the same with varying results. However, I was looking for something that I could run from the command line and didn’t contain a thick client to run.
This is when I stumbled across Gobuster. It was everything I was looking for in a command-line-driven web enumeration tool. I can quickly switch between directory brute forcing and virtual host enumeration. I can switch wordlists on the fly, set command-line arguments to perform file detection, and finally, adjust the thread count. All these features are why I personally have been using Gobuster during pentest engagements.
If you encounter below error while using GoBuster:
GoBuster: command not found
you may try installing below package as per your choice of distribution.
| Distribution | Command |
|---|---|
| OS X | brew install gobuster |
| Debian | apt-get install gobuster |
| Ubuntu | apt-get install gobuster |
| Kali Linux | apt-get install gobuster |
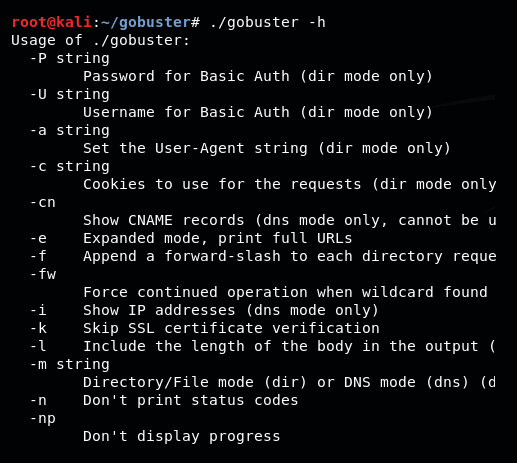
To view available options with GoBuster command:
Summary
Gobuster can be used to brute-force URIs and DNS subdomains from the command line. (If you prefer a graphical user interface, check out OWASP’s Dirbuster.) In Gobuster, you can use wordlists for common directories and subdomains to automatically request every item in the wordlist, send the items to a web server, and filter the interesting server responses. The results generated from Gobuster will provide you with the URL path and the HTTP status response codes. (While you can brute-force URIs with Burp Suite’s Intruder, Burp Community Edition is much slower than Gobuster.)